Is platform-provided security enough to secure APIs?
API security is a critical aspect of any organization's overall security strategy. APIs [...]
How Your Attack Surface Changes When Moving To Cloud Native Apps
Nothing has had a bigger impact on how we look at web app [...]
The data you’re missing to shift left is in runtime
The web application development industry is driven by data. Every decision we make [...]
Why web application & API security go hand in hand
Your dev team is probably working on an application right now that relies [...]
The 3 Biggest Misconceptions About Application & API Security
Application development environments are evolving quicker than ever before. This also means the [...]
Key Elements to Protecting Your Software Supply Chain
Open source code is everywhere. Most software companies on planet earth use open [...]
Agent vs Agentless, and the In-Between
In the past several years AppSec agents have gotten a bad rep, perhaps [...]
Everything You Need To Know About API Rate Limiting
There are many approaches to API security, but API rate limiting is arguably [...]
The 7 Best Practices for a Successful DevSecOps Life Cycle
Understanding the importance of DevSecOps for web application security is vital for today’s [...]
How to prevent DDoS attacks on APIs
There’s nothing more threatening to your APIs than a DDoS attack. This [...]
What Is Devsecops? Why It’s Hard To Do Well
There’s a sea change happening in the world of software development. The rapid [...]
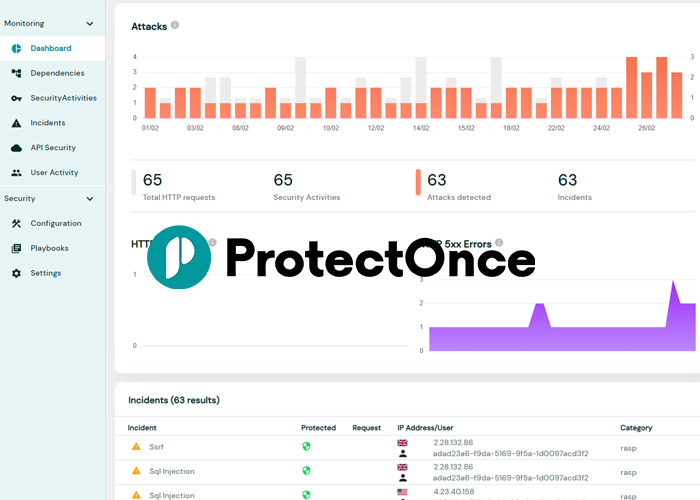
Why is ProtectOnce different?
Shifting Runtime Security Left For the past few years, AppSec has been all [...]
How to Detect a log4j Vulnerability in a Web Application
The log4j vulnerability was discovered as a zero-day exploit in late 2021. It’s [...]
How Do You Prevent Remote Code Execution Attacks?
Remote code execution attacks are a serious threat to modern web applications and [...]
The Ultimate Node.js Security Checklist
Statistics on market usage reveal that Node.js is now the main framework for [...]
OWASP’s Automated Threats to Web Applications Explained
Many businesses rely on web applications because of their accessibility across multiple users, [...]
It’s the end of the WALL as we know it
For about 10000 years, humans built walls around their cities. Walls constituted a [...]
A Quick SOC 2 Compliance Guide To Get You Started
Many companies don't know where to start when it comes to SOC 2 [...]
Your Guide To Mobile Application Security
New technology means new opportunity, but it also means new security risk. With [...]
What is Web Application Security Testing Why Its Hard to Do Well
Organizations are moving to web-based applications and websites to reach customers directly and [...]
9 API Security Best Practices Devs Need to Know
If you had to guess, what would you say are the API security [...]
5 Best Practices to Prevent SQL Injection Attacks
Since August of 2021, a new wave of mass SQL injection attacks has [...]
WAF vs RASP? Wrong…
A Brief History of AppSec In the beginning, there were just firewalls. Then [...]
The 10 Best Practices for Serverless Security
Today, most cloud service providers are offering robust cloud services through serverless security [...]